Each new protocol introduces its personal complexities. When a brand new protocol exhibits up, the primary query to ask is whether or not it’s really needed. So, let’s ask that query concerning the mannequin context protocol (MCP).
The present wave of agentic apps, sparked by instruments like ChatGPT, are powered by giant language fashions (LLMs) that excel at duties like summarization, content material creation, and picture processing however include elementary limitations. Specifically:
- No entry to real-time information
- No entry to non-public information
- No potential to execute instruments
MCP addresses the above limitations by appearing as a common protocol that connects agentic apps to real-world information and instruments. However it’s honest to ask, why introduce a brand new protocol after we have already got safe and high-performing APIs?
The quick reply is that, whereas right this moment’s highly effective APIs could be linked to agentic apps, there’s a problem. These APIs differ extensively, e.g. REST, GraphQL, gRPC, utilizing HTTP, WebSockets, Pub/Sub. Their auth mechanisms differ too, e.g. API keys, OAuth2. Which means every integration is bespoke. Builders should learn docs, construct flows, and wire up APIs one after the other.
WSO2
This static integration mannequin is confirmed however doesn’t match the dynamic nature of agentic apps. That’s the place MCP is available in. MCP defines clear client-server roles, a typical protocol format, and a life cycle, primarily turning into the common connector between LLMs and exterior techniques. So you’ll be able to consider MCP because the USB-C within the API world.
How MCP works
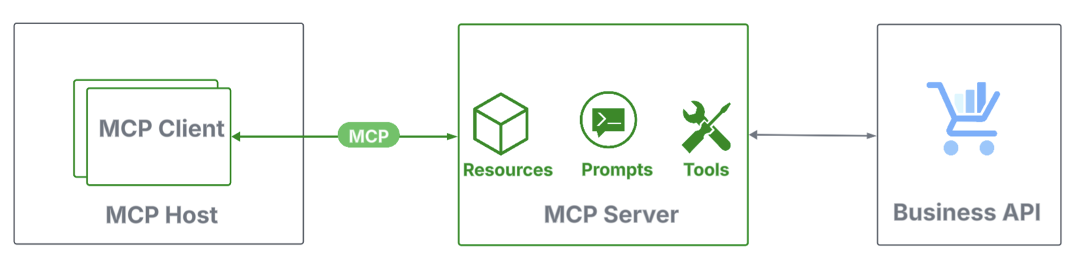
MCP defines three core roles—a bunch, a shopper, and a server:
- Host: Agentic functions that handle shopper life cycles and implement safety.
- Consumer: Light-weight connectors inside hosts that set up a 1:1 session with an MCP server.
- Server: Applications that join MCP purchasers to information sources and instruments, both regionally or remotely.
WSO2
Every position offers a set of options. MCP servers expose sources (contextual information like calendar occasions), prompts (structured templates that information person enter to enhance LLM output), and instruments (executable capabilities). MCP purchasers hook up with MCP servers to request information, execute instruments, and orchestrate brokers.
MCP makes use of JSON-RPC, a light-weight, structured protocol for requests and responses, and defines two commonplace transport mechanisms for client-server communication, commonplace enter and output (STDIO) and streamable HTTP.
Securing a neighborhood MCP server
When the MCP server runs regionally, the STDIO transport needs to be used. In apply, this implies the agentic app launches the MCP server as a sub-process and communicates by way of its commonplace enter and output streams. As a result of this communication stays fully inside the native system, it’s inherently safe, and the MCP auth spec doesn’t require any extra safety.
WSO2
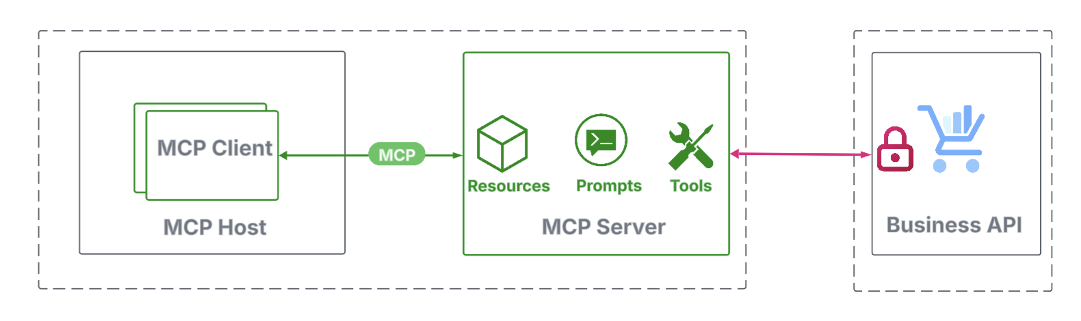
Nonetheless, when an MCP server communicates with back-end APIs, usually over the web, safety turns into a high precedence, however falls outdoors the scope of the MCP auth specification. However, there’s nonetheless no want for brand new mechanisms; current API safety practices suffice. Widespread approaches embody:
- Lengthy-lived tokens: API keys and tokens, legitimate for days or months, are obtained through out-of-band channels and configured within the MCP server.
- Quick-lived tokens: With lifespans underneath an hour, short-lived tokens can’t be set manually. As a substitute, the MCP server should dynamically request them at run time with person approval. OAuth2 entry tokens and JWTs are typical examples.
Securing a distant MCP server
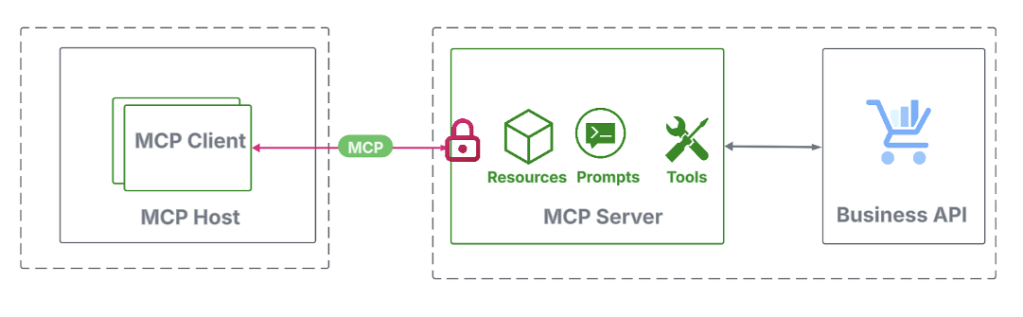
An MCP shopper connects to a distant MCP server through HTTP by initiating a request to its endpoint URL. As specified by the MCP auth spec, this endpoint should be OAuth 2.1-protected, requiring the shopper to current a legitimate entry token.
WSO2
The MCP auth spec outlines a token acquisition course of designed to assist dynamic, agentic integrations. These interactions embody the next steps.
WSO2
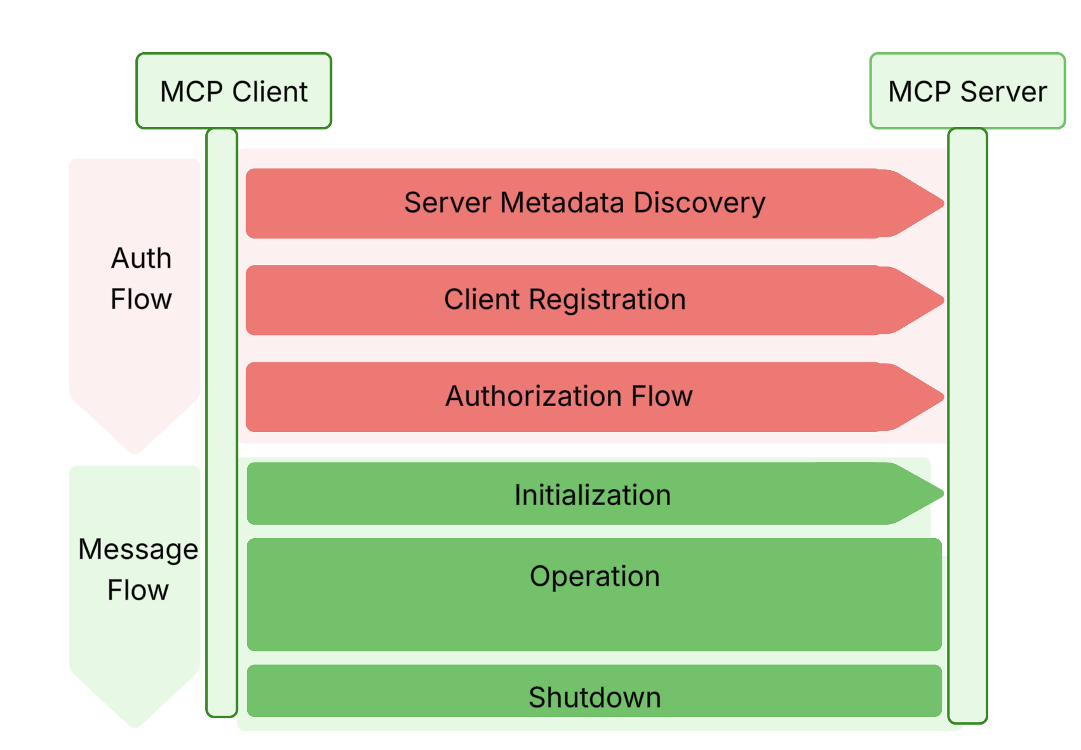
Server metadata discovery
As soon as the MCP server URL is offered as a configuration parameter, the shopper constructs a server metadata endpoint by eradicating any path elements and appending a /well-known/oauth-authorization-server path. The shopper then retrieves a JSON-formatted server metadata doc from this endpoint. Each the endpoint and the doc should adjust to the OAuth 2.0 Authorization Server Metadata specification. This metadata helps the shopper uncover the next info required in the course of the subsequent steps:
- Registration endpoint
- Authorization and token endpoints
- Supported grant sorts and scopes
Deriving the server metadata endpoint from the MCP server URL was meant to let purchasers function with a single configuration parameter. Nonetheless, this tightly {couples} the authorization and useful resource server roles, limiting using current OAuth 2.0 infrastructure and purpose-built id options. To deal with this, the upcoming MCP auth spec replaces this mechanism with the OAuth 2.0 Protected Useful resource Metadata specification.
Consumer registration
Primarily based on the knowledge retrieved from the server metadata doc, the shopper software sends a registration request to the shopper registration endpoint. The MCP auth specification adopts the OAuth 2.0 Dynamic Consumer Registration (DCR) protocol to register the shopper as an OAuth 2.1 shopper. Within the DCR response, the shopper software receives a client_id and, for confidential purchasers, a client_secret. Each are required for the following step.
Whereas DCR is extensively adopted, opinions differ on open registration, and the spec itself permits defending the registration endpoint with OAuth 2.0. Once more, to assist single-parameter configuration, the MCP auth spec recommends open registration. It stays to be seen how this can evolve.
Entry token retrieval
At this stage, the shopper has all the things wanted to request an entry token. Relying on the use case, one of many following OAuth 2.1 grant sorts is used:
- Consumer Credentials: If the shopper software is accessing the MCP server straight, it makes use of the Consumer Credentials grant with the
client_idandclient_secretobtained throughout registration, together with the token endpoint and scopes found from the server metadata. - Authorization Code: If the shopper accesses the MCP server on behalf of an finish person, it makes use of the Authorization Code grant. This circulation requires the
client_idandclient_secretfrom registration and the authorization endpoint, token endpoint, and scopes from the server metadata. Moreover, as required by OAuth 2.1, the shopper should use Proof Key for Code Trade (PKCE) to boost safety.
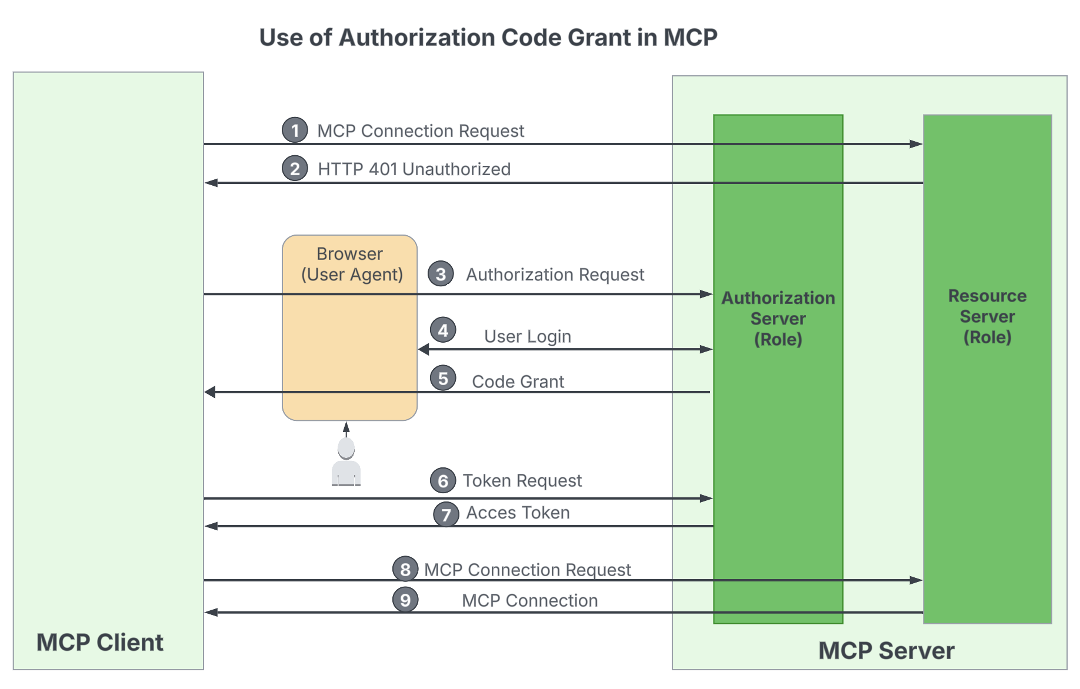
WSO2
If all the things goes nicely, the shopper software obtains a legitimate entry token and might provoke a connection request to the MCP server URL, passing the token through the Authorization HTTP header. The MCP server then validates the token and establishes the connection if it’s legitimate.
In the end, this safety circulation aligns with typical OAuth-based API safety flows, apart from the preliminary step of deriving the server metadata URL from the MCP server URL.
Sagara Gunathunga is director of options structure at WSO2.
—
Generative AI Insights offers a venue for know-how leaders to discover and talk about the challenges and alternatives of generative synthetic intelligence. The choice is wide-ranging, from know-how deep dives to case research to professional opinion, but in addition subjective, primarily based on our judgment of which matters and coverings will finest serve InfoWorld’s technically refined viewers. InfoWorld doesn’t settle for advertising collateral for publication and reserves the suitable to edit all contributed content material. Contact doug_dineley@foundryco.com.

