Cybercriminals are exploiting the current vital LDAP vulnerabilities (CVE-2024-49112 and CVE-2024-49113) by distributing pretend proof-of-concept exploits for CVE-2024-49113 (dubbed “LDAPNightmare”).
These malicious PoCs, typically disguised as instruments to exhibit the vulnerability’s influence, are designed to trick safety researchers and system directors into downloading and executing them.
When these malicious information are executed, they as an alternative set up malware that steals info on the system of the sufferer, which provides the attackers entry to delicate knowledge.
The high-profile nature of the LDAP vulnerabilities is utilized on this assault with a purpose to improve the probability that victims will fall for the lure.
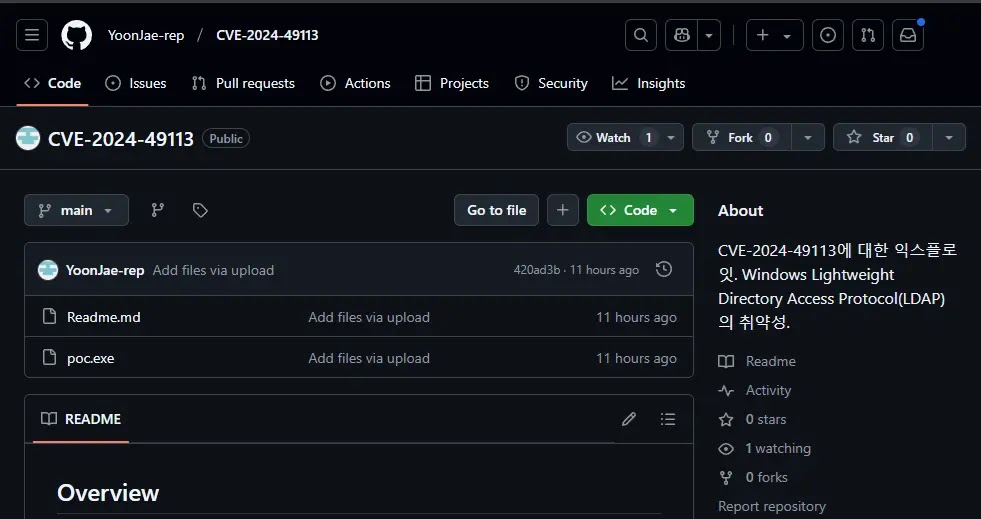
A malicious actor forked a reputable Python repository after which changed the unique Python supply code information with a packed executable (poc.exe) possible created utilizing UPX.
Examine Actual-World Malicious Hyperlinks, Malware & Phishing Assaults With ANY.RUN – Strive for Free
This substitution is very suspicious, as executables aren’t sometimes discovered inside Python tasks, which primarily depend on Python scripts, as this surprising presence of an executable strongly signifies malicious exercise inside the repository.
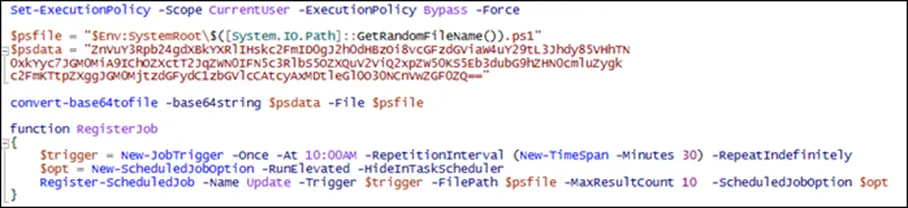
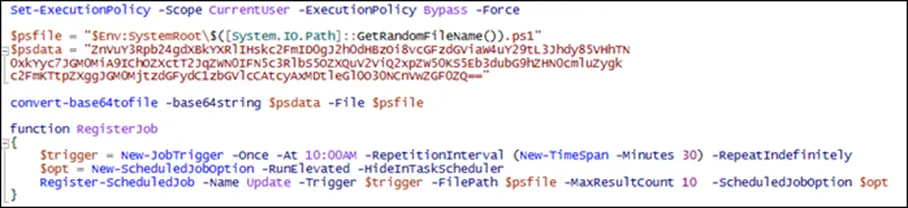
Upon execution, the file drops and executes a PowerShell script within the %Temp% listing and establishes a persistent an infection by making a scheduled job that triggers the execution of an encoded script.
After decoding, this script fetches one other script from Pastebin and the ultimate script acquires the sufferer’s public IP deal with and exfiltrates it to an exterior server by way of FTP, possible for additional exploitation or command-and-control functions.
The process entails amassing delicate system knowledge, together with pc specs, operating processes, listing contents, community configurations (IPs and adapters), and put in updates, which is then compressed utilizing the ZIP algorithm for environment friendly storage.
The compressed knowledge is then uploaded to an exterior FTP server utilizing credentials which were pre-defined, which can end in delicate system info being accessed by unauthorized events.
To mitigate the danger of downloading malware from pretend repositories, prioritize downloading code from official and trusted sources. Scrutinize repositories with suspicious content material, particularly these with few stars, forks, or contributors, regardless of claims of widespread use.
Confirm the repository proprietor’s identification each time doable and conduct thorough opinions of commit historical past and up to date modifications for anomalies. Examine the repository’s dialogue boards and situation trackers for potential pink flags.
In accordance with Pattern Micro, by implementing these measures, builders can considerably scale back the probability of introducing malicious code into their tasks.
Discover this Information Fascinating! Comply with us on Google Information, LinkedIn, and X to Get Instantaneous Updates!

