Seventy-seven malicious Android apps with greater than 19 million installs had been delivering a number of malware households to Google Play customers.
This malware infiltration was found by Zscaler’s ThreatLabs crew whereas investigating a brand new an infection wave with Anatsa (Tea Bot) banking trojan focusing on Android gadgets.
Whereas a lot of the malicious apps (over 66%) included adware parts, the commonest Android malware was Joker, which researchers encountered in nearly 25% of the analyzed apps.
As soon as Joker malware is put in on a tool, it will probably learn and ship textual content messages, take screenshots, make telephone calls, and steal contact lists, entry gadget info, and subscribe customers to premium companies.
A smaller proportion of the apps included maskware, a time period used to outline a malicious app that disguises itself as one thing that may not increase any suspicion.
Such a malware could pose as a authentic app that works as marketed. Nevertheless, it performs malicious exercise within the background, corresponding to steal credentials, banking information, or different delicate knowledge (location, SMS). Cybercriminals also can use maskware to ship different malware.
Zscaler researchers additionally discovered a variant of the Joker malware referred to as Harly, which comes as a authentic app that has a malicious payload hidden deeper within the code to keep away from detection through the evaluate course of.

In a report in March, Human Safety researchers mentioned that Harly can cover in in style apps, like video games, wallpapers, flashlights, and picture editors.
Anatsa trojan retains evolving
In line with Zscaler, the newest model of the Anatsa banking trojan has additional expanded its focusing on scope, growing the variety of banking and cryptocurrency apps to 831, from 650 beforehand, that it makes an attempt to steal knowledge from.
The malware operators use an app named ‘Doc Reader – File Supervisor’ as a decoy, which solely downloads the malicious Anatsa payload after set up, to evade Google’s code evaluate.
Supply: Zscaler
The newest marketing campaign has switched from distant DEX dynamic code loading used up to now to direct payload set up, unpacking it from JSON information, after which deleting them.
By way of evasion, it makes use of malformed APK archives to interrupt static evaluation, runtime DES-based string decryption, and emulation detection. Package deal names and hashes are additionally periodically modified.
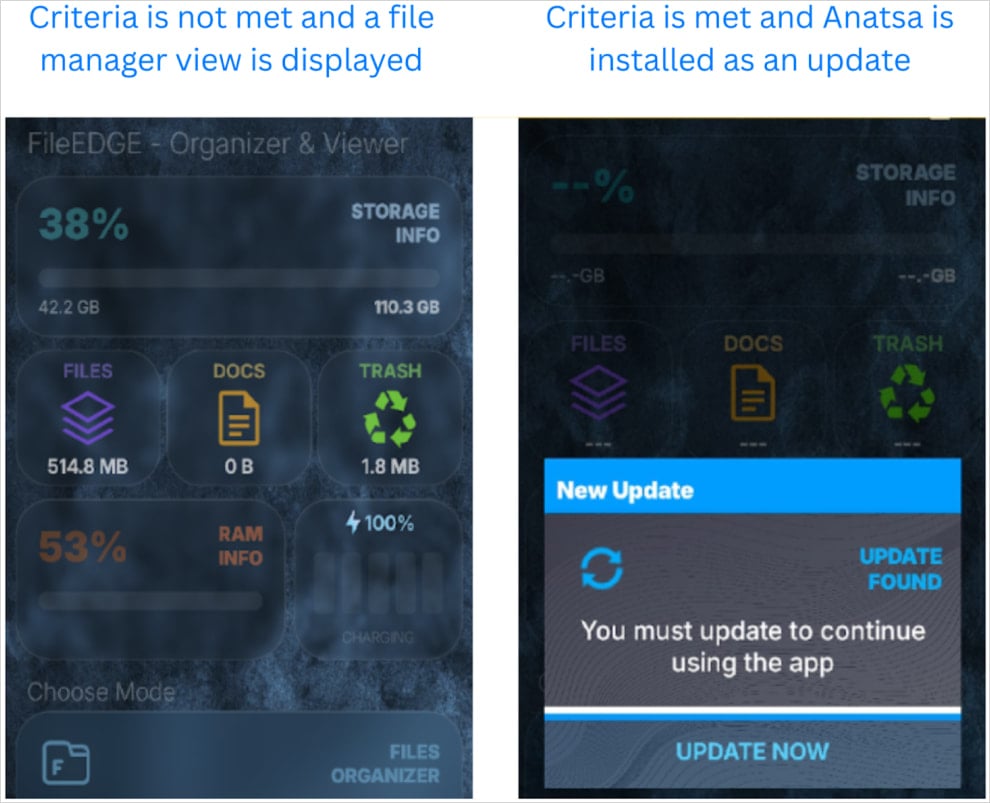
Supply: Zscaler
Functionality-wise, Anatsa abuses Accessibility permissions on Android to auto-grant itself intensive privileges.
It fetches phishing pages from its server for over 831 apps, now additionally protecting Germany and South Korea, whereas a keylogger module has additionally been added for generic knowledge theft.
This newest Anatsa marketing campaign follows one other current wave found by ThreatFabric in July, the place the trojan sneaked into Google Play posing as a PDF viewer, reaching over 50,000 downloads.
Older Anatsa campaigns embrace a PDF and QR Code Reader assault in Could 2024 that achieved 70,000 infections, a Cellphone Cleaner and PDF assault in February 2024 that acquired 150,000 downloads, and one other PDF Viewer assault in March 2023 that achieved 30,000 installs.
Malicious app wave on Google Play
Along with the malicious Anatsa apps, Zscaler found this time, most had been adware households, adopted by ‘Joker,’ ‘Harly,’ and varied maskware.
“ThreatLabz recognized a pointy rise in adware functions on the Google Play Retailer alongside malware, corresponding to Joker, Harly, and banking trojans like Anatsa,” defined Zscaler researcher Himanshu Sharma
“Conversely, there was a noticeable decline in malware households corresponding to Facestealer and Coper.”
Instruments and personalization apps accounted for over half of the lures used to unfold these apps, so these two classes, along with leisure, pictures, and design, must be handled as high-risk.
In complete, the 77 malicious apps, together with these containing Anatsa, had been downloaded 19 million instances from Google Play.
Zscaler stories that Google eliminated all the malicious apps they found this time from the Play Retailer following their reporting.
Android customers should guarantee their Play Defend service is energetic on their gadget to flag malicious apps for removing.
Within the case of Anatsa trojan infections, separate steps have to be taken with the financial institution to guard probably compromised e-banking accounts or credentials.
To attenuate the chance from malware loaders on Google Play, solely belief respected publishers, learn not less than a few consumer opinions, and solely grant permissions which are instantly associated to the app’s core performance.


