[ad_1]
On this blogpost, we offer a technical evaluation of CloudScout, a post-compromise toolset utilized by Evasive Panda to focus on a authorities entity and a spiritual group in Taiwan from 2022 to 2023. The CloudScout toolset is able to retrieving information from numerous cloud companies by leveraging stolen net session cookies. By means of a plugin, CloudScout works seamlessly with MgBot, Evasive Panda’s signature malware framework.
Key factors of this blogpost:
- The CloudScout toolset was detected in Taiwan, between 2022 and 2023, within the community of a spiritual establishment and at a authorities entity.
- CloudScout makes use of stolen cookies, offered by MgBot plugins, to entry and exfiltrate information saved at numerous cloud companies.
- We analyzed three CloudScout modules, which goal to steal information from Google Drive, Gmail, and Outlook. We consider that at the least seven further modules exist.
- Hardcoded fields in CloudScout’s net requests for stealing Outlook electronic mail messages counsel that the samples concerned had been crafted to focus on Taiwanese customers.
- Every CloudScout module, programmed in C#, is deployed by an MgBot plugin, programmed in C++.
Evasive Panda profile
Evasive Panda (also referred to as BRONZE HIGHLAND, Daggerfly, or StormBamboo) is a China-aligned APT group, working since at the least 2012. Evasive Panda’s goal is cyberespionage in opposition to international locations and organizations opposing China’s pursuits via independence actions corresponding to these within the Tibetan diaspora, non secular and tutorial establishments in Taiwan and in Hong Kong, and supporters of democracy in China. At instances now we have additionally noticed its cyberespionage operations lengthen to international locations corresponding to Vietnam, Myanmar, and South Korea.
Evasive Panda has amassed a powerful listing of assault vectors. We’ve got seen its operators conduct refined TTPs corresponding to supply-chain and watering-hole assaults, and DNS hijacking; as well as, they’ve abused the newest CVEs affecting Microsoft Workplace, Confluence, and net server functions. The group additionally demonstrates a robust functionality for malware growth, which is showcased in its deep assortment of multiplatform backdoors for Home windows, macOS, and Android. For Home windows, its most-used instruments are MgBot (since 2012; a {custom} malware framework consisting of a principal implant and eight presently recognized plugins as detailed in our WLS blogpost) and the extra lately developed Nightdoor (described in one other WLS blogpost; a feature-rich backdoor that makes use of public cloud companies for C&C communications).
Overview
In early 2023, we detected Evasive Panda deploy three beforehand unknown .NET modules (internally named CGD, CGM, and COL) at a authorities entity in Taiwan. These modules are designed to entry public cloud companies corresponding to Google Drive, Gmail, and Outlook by hijacking authenticated net periods. This system depends on stealing cookies from an internet browser database, then utilizing them in a selected set of net requests to realize entry to cloud companies. Not like stolen credentials, which can be blocked by safety features corresponding to two-factor authentication (2FA) and IP monitoring, stolen net session cookies enable the attacker to retrieve information saved within the cloud, proper from the sufferer’s machine. In 2023, Google launched the Gadget Certain Session Credentials (DBSC) challenge on GitHub and, in 2024, the App-Certain Encryption characteristic within the Chrome 127 replace. These are protecting measures in opposition to cookie-theft malware, corresponding to CloudScout, and will probably render this toolset out of date.
Additional code evaluation of the three modules reveals an underlying growth framework, codenamed CloudScout by its builders. On this blogpost, we offer an in depth evaluation of this modular framework programmed in C#. To the very best of our data, the CloudScout toolset has not beforehand been documented publicly.
Victimology
In response to ESET telemetry, CloudScout was noticed in two incidents concentrating on Taiwan:
- In Could 2022, the community of a Taiwanese non secular establishment was compromised with MgBot and Nightdoor. On this incident, MgBot was used to put in a plugin that deploys a CloudScout module.
- In February 2023, CloudScout modules and the Nightdoor implant had been detected at what we suspect is a Taiwanese authorities entity.
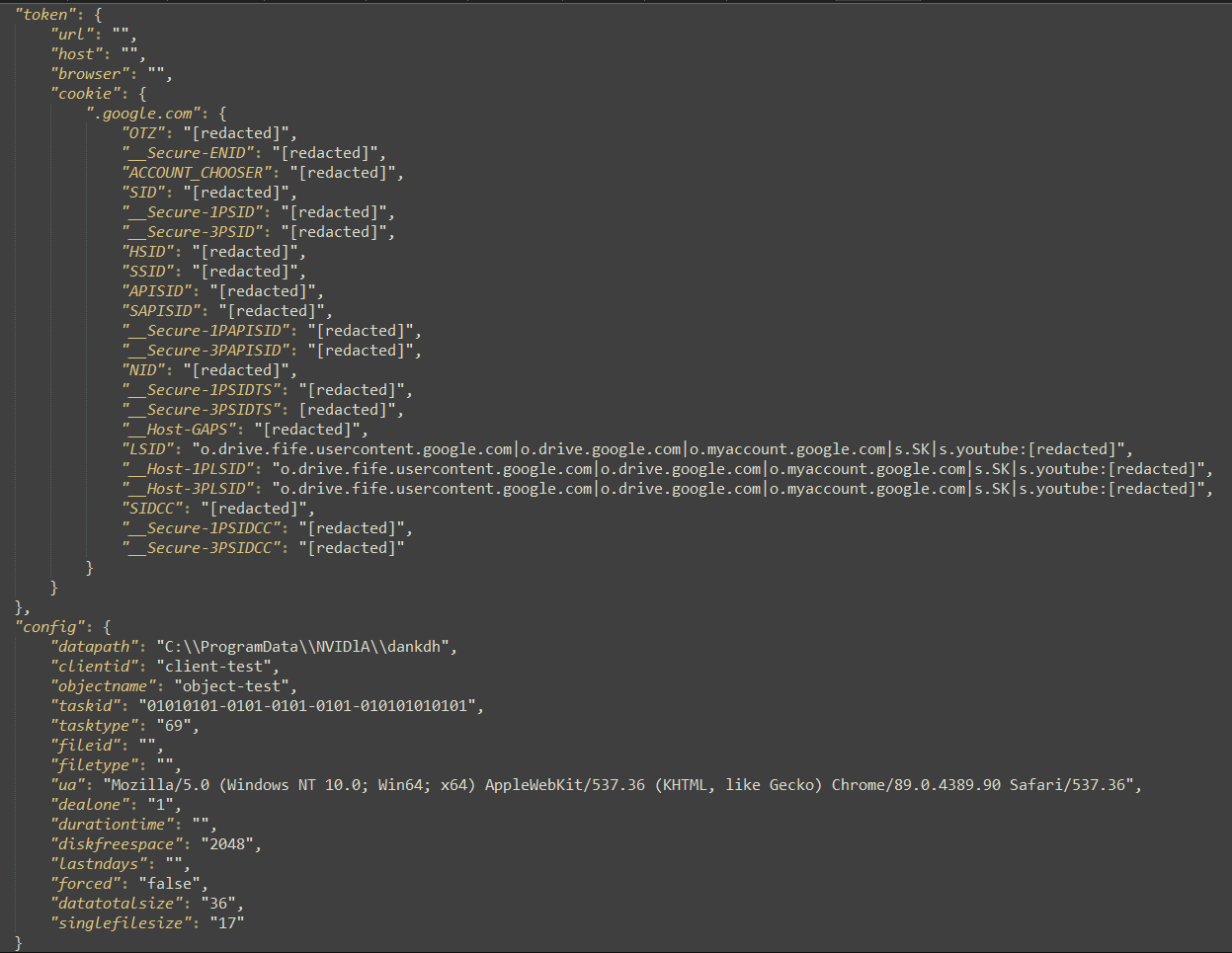
Moreover, we present in some hardcoded HTTP requests the inclusion of Taipei Commonplace Time because the time zone and zh-CN because the language pack (as proven in Determine 1). Each counsel that these samples had been crafted to focus on Taiwanese customers.
Technical evaluation
CloudScout is a .NET malware framework consisting of a number of modules concentrating on completely different cloud companies. The title CloudScout originated from the PDB paths of the modules obtained:
- E:projectgit_newMProjectsCodeCloudScoutGoogleDriverCGDobjDebugCGD.pdb
- E:projectgit_newMProjectsCodeCloudScoutGmailCGMobjDebugCGM.pdb
- E:projectgit_newMProjectsCodeCloudScoutOutlookCOLobjDebugCOL.pdb
We additionally discovered point out of seven different modules within the framework (see the part CommonUtilities: The center of CloudScout); on the time of writing, now we have not but noticed them deployed on compromised machines, hinting that the attackers deploy them selectively. Altogether, the whole listing of CloudScout modules is:
- CGD
- CGM
- COL
- CTW
- CFB
- GMQ
- MEXC
- CEXC
- CZI
- CNE
Primarily based on the naming conference (e.g., the module concentrating on Google Drive is known as CGD, the one concentrating on Gmail CGM, and the one concentrating on Outlook COL), we infer that CTW and CFB presumably goal Twitter and Fb. Nevertheless, the aim of different modules stays undetermined.
Improvement timing
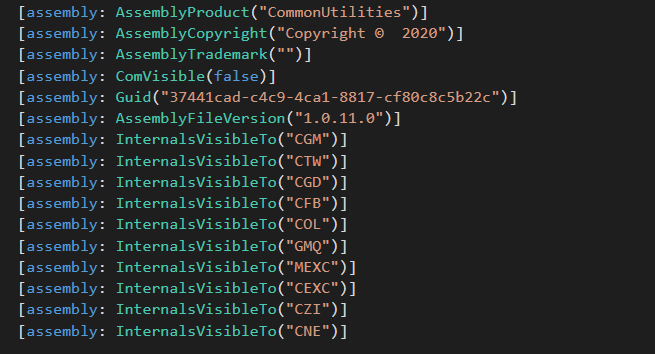
The AssemblyCopyright area’s worth, Copyright © 2020, within the .NET manifest of CloudScout modules, as seen in Determine 2, means that the CloudScout toolset might need been developed round 2020. Despite the fact that the legitimacy of the .NET manifest is questionable, it’s constant throughout all of the samples that we discovered. As well as, completely different variations said within the AssemblyVersion of CGD and CGM mirror the adjustments added to their code base.
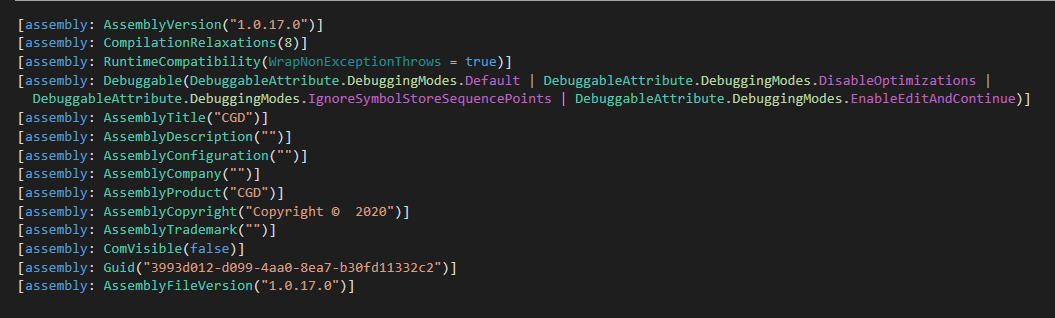
We additionally discovered completely different variations of the embedded inner custom-made library package deal CommonUtilities. Desk 1 exhibits completely different variations of CGD, CGM, and COL containing completely different variations of CommonUtilities.
Desk 1. Variations of CloudScout modules
| Module | Model | SHA-1 | CommonUtilities model |
| CGD | 1.0.11 | 67028AEB095189FDF18B2D7B775B62366EF224A9 | 1.0.08 |
| 1.0.14 | B3556D1052BF5432D39A6068CCF00D8C318AF146 | 1.0.10 | |
| 1.0.17 | 84F6B9F13CDCD8D9D15D5820536BC878CD89B3C8 | 1.0.11 | |
| CGM | 1.0.11 | 4A5BCDAAC0BC315EDD00BB1FCCD1322737BCBEEB | 1.0.08 |
| 1.0.13 | C058F9FE91293040C8B0908D3DAFC80F89D2E38B | 1.0.10 | |
| 1.0.14 | 621E2B50A979D77BA3F271FAB94326CCCBC009B4 | 1.0.11 | |
| COL | 1.0.10 | 93C1C8AD2AF64D0E4C132F067D369ECBEBAE00B7 | 1.0.08 |
Assuming that the .NET manifest is correct, in 2020 alone, we noticed three new toolsets from Evasive Panda. The opposite two cases are the primary look of Nightdoor and a brand new UDP variant of MgBot (succeeding the UDT variant).
Previous canine, new methods
From a typical RC4 encryption key shared by the three modules, we carried out a retrohunt and found that CGM was deployed by an MgBot plugin known as Gmck.dll, which was programmed in C++. The plugin was detected in an incident in 2022 the place two machines from the aforementioned non secular establishment in Taiwan had been compromised by Evasive Panda. In that incident (illustrated in Determine 3), MgBot put in the CGM module, which in flip accessed the sufferer’s Gmail account to obtain emails and private info.
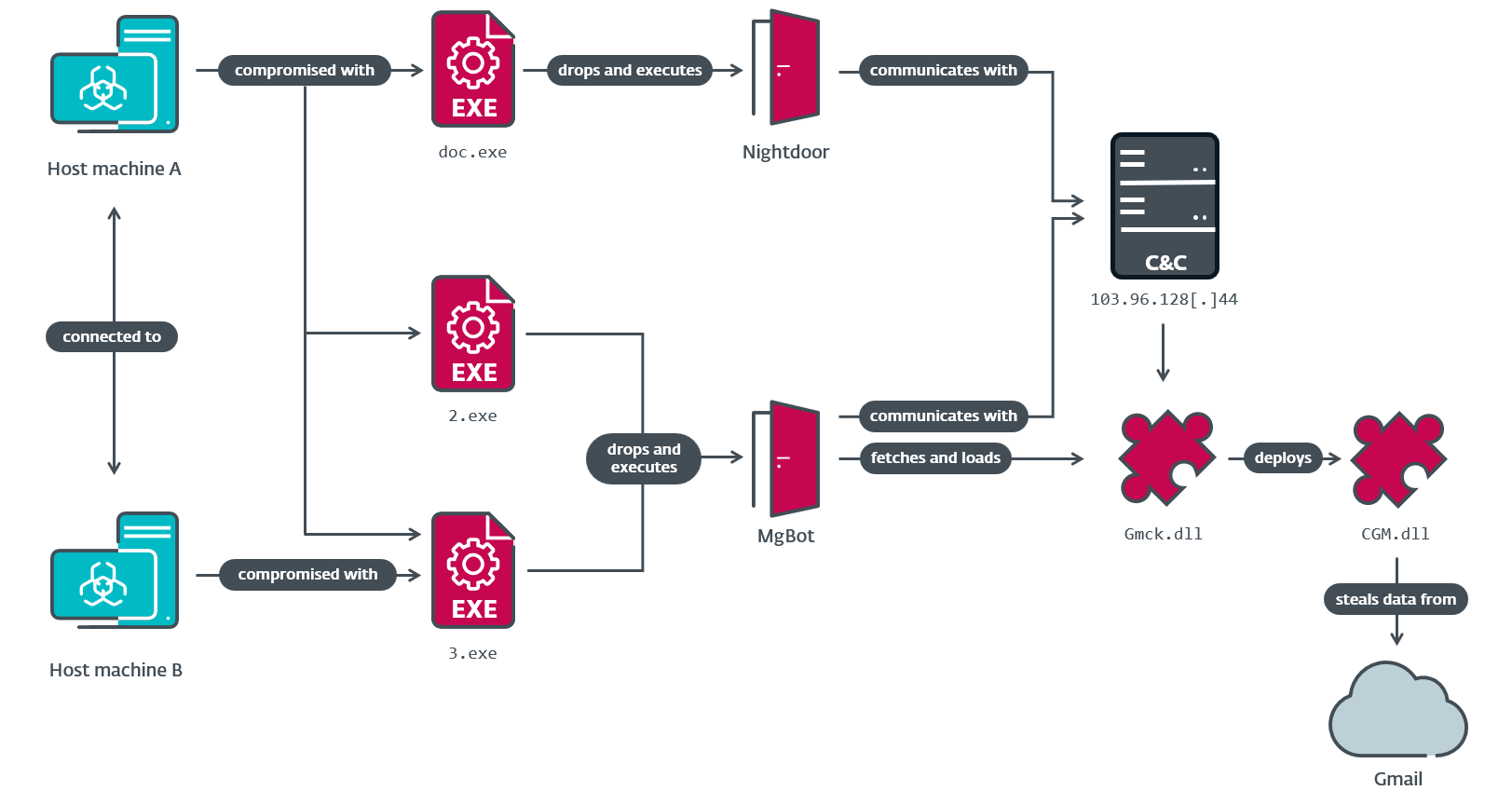
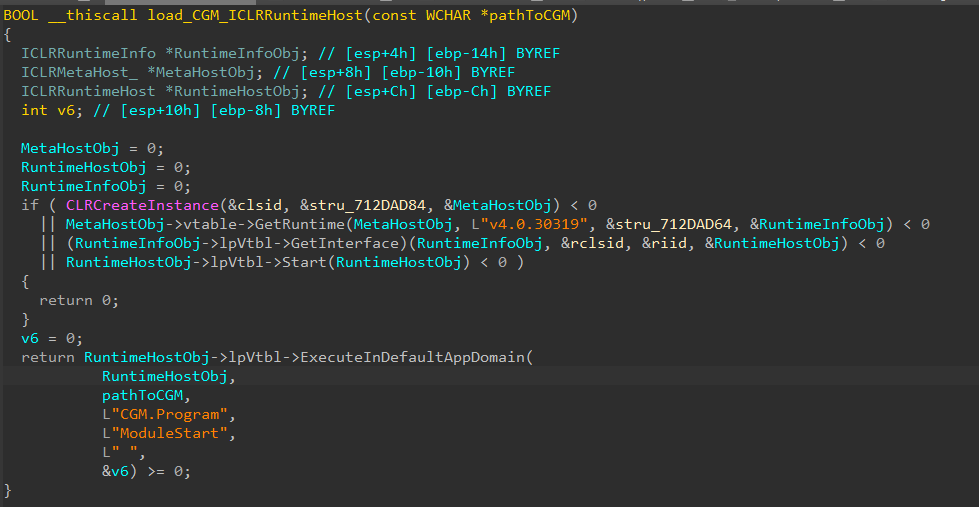
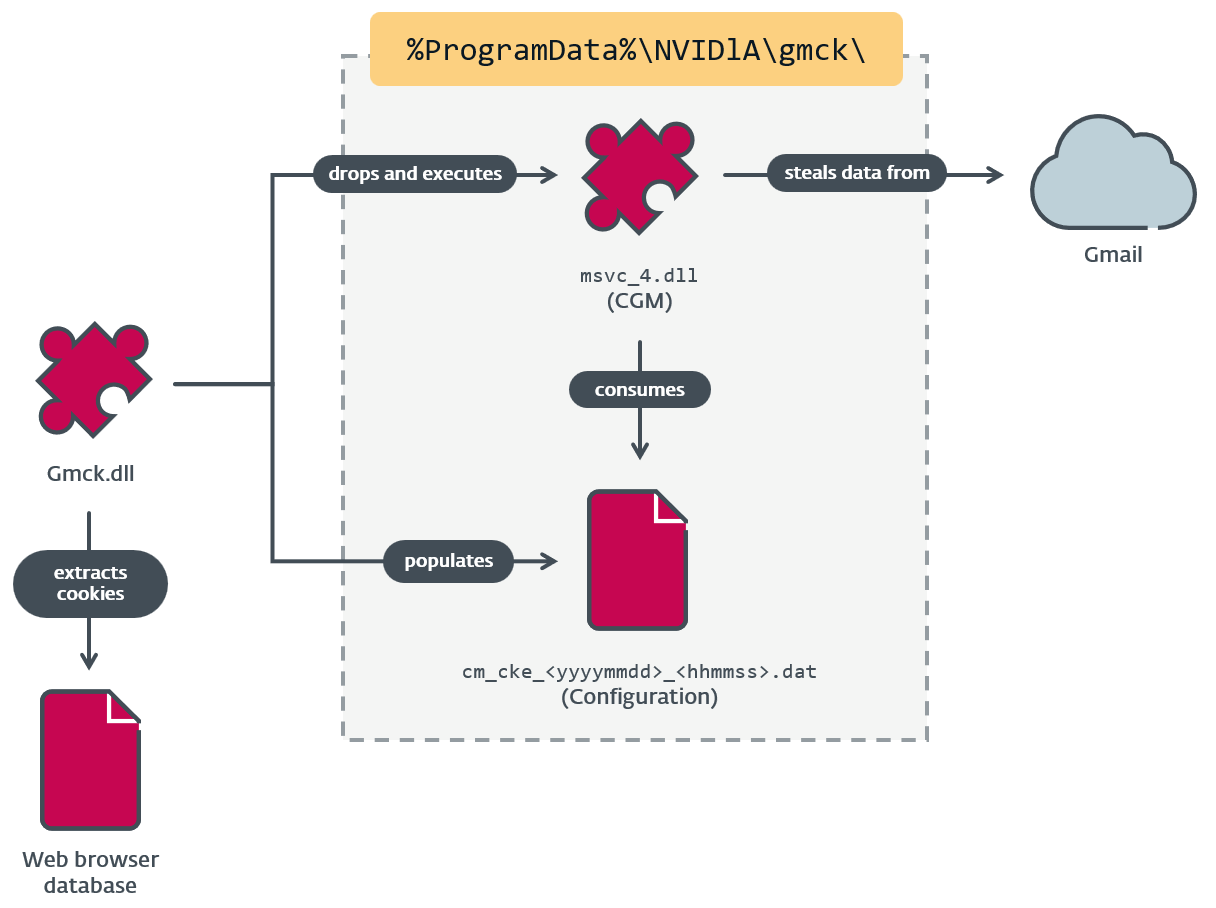
Gmck.dll (which we are going to consult with as Gmck) carries the .NET module CGM inside its binary. As a way to execute CGM, Gmck first drops the module to disk at a hardcoded path, then begins the widespread language runtime (CLR) utilizing ICLRMetaHost and ICLRRuntimeHost. Lastly, it calls ExecuteInDefaultAppDomain with a reference to CGM’s entry level perform (ModuleStart), as seen in Determine 4.
In response to our telemetry, CGD and COL modules are additionally written to the identical staging folder, as proven in Desk 2.
Desk 2. Paths the place CloudScout modules are deployed
| MgBot plugin | Deployment path | CloudScout module |
| Gmck.dll | %ProgramDatapercentNVIDlAgmckmsvc_4.dll | CGM |
| N/A | %ProgramDatapercentNVIDlAolckmsvc_4.dll | COL |
| N/A | %ProgramDatapercentNVIDlAdankdhmsvc_4.dll | CGD |
The staging folder NVIDlA is purposely misspelled utilizing a easy homograph: it’s all in uppercase letters besides that the letter after the D is a lowercase letter el. The subfolders (as highlighted) appear to be named after the MgBot plugins. Sadly, now we have been unable to acquire the olck and dankdh plugins.
After the CGM module is efficiently deployed, the Gmck plugin wants to supply browser cookies to CGM within the type of a configuration file. Gmck extracts these cookies from net browser database recordsdata listed in Desk 3. With the discharge of App-Certain Encryption in Chrome 127 and Edge 128, Gmck is not in a position to decrypt Cookies database recordsdata from Chrome and Edge.
Desk 3. Database recordsdata from which Gmck extracts cookies
| Focused browser | Database recordsdata |
| Chrome | %localappdatapercentGoogleChromeUser DataLocal State %localappdatapercentGoogleChromeUser Information |
| Edge | %localappdatapercentMicrosoftEdgeUser DataLocal State %localappdatapercentMicrosoftEdgeUser Information |
| Firefox | %AppDatapercentMozillaFirefoxprofiles.ini %AppDatapercentMozillaFirefox |
The configuration file should have a .dat extension and be RC4 encrypted utilizing the important thing 0dda5a8d-e4c2-477d-85df-fcb611a62ffe to be able to be acknowledged by CGM. This RC4 key’s utilized by all three CloudScout modules to decrypt the configuration recordsdata, which suggests the MgBot plugins should additionally use this key for encryption.
Determine 5 summarizes the connection between Gmck and CGM.
Configuration
The configuration file cm_cke_
The configuration file is in JSON format. It accommodates two principal information buildings: token and config. The token construction accommodates the cookies organized by area title. And config accommodates settings for downloading and staging the collected information for exfiltration, in addition to for protecting this system operating or exiting after a profitable cycle (dealone area). An instance of a configuration file is included in Determine 6.
CommonUtilities: The center of CloudScout
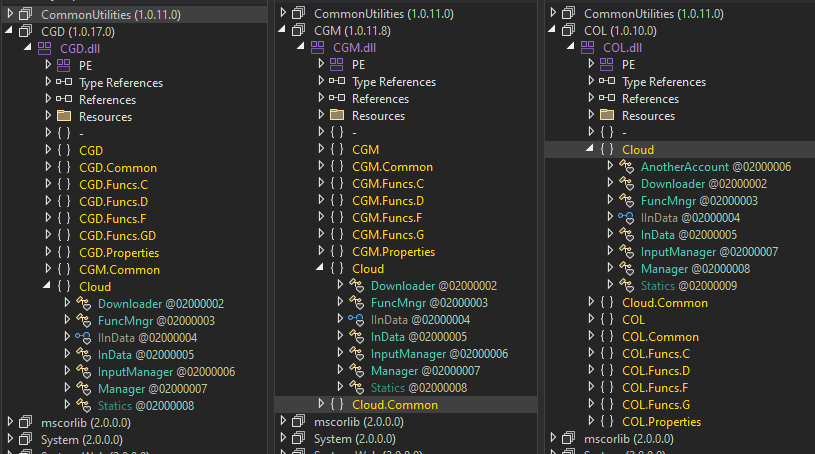
On the coronary heart of CloudScout is the CommonUtilities package deal, which offers all mandatory low-level libraries for the modules to run, as illustrated in Determine 7. This package deal is saved within the sources part of CloudScout modules and is loaded firstly of the ModuleStart perform.
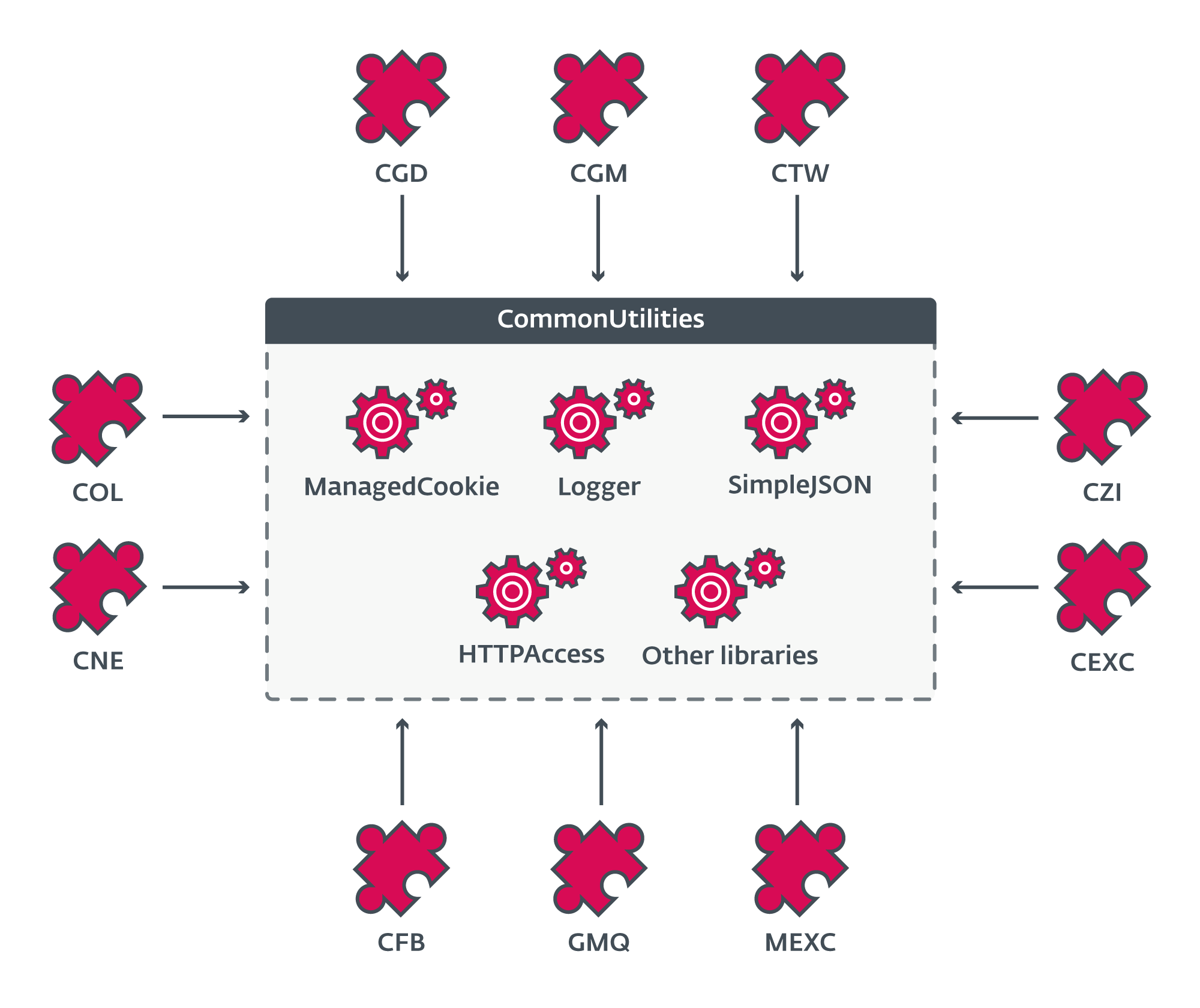
As seen in Determine 8, the .NET manifest of CommonUtilities reveals all of its consumer modules.
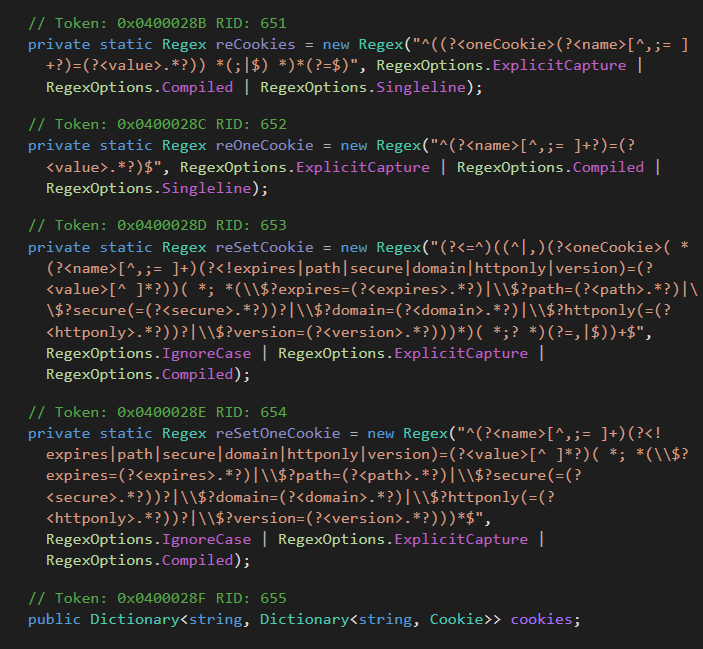
CommonUtilities accommodates fairly a couple of custom-implemented libraries regardless of the plentiful availability of comparable open-source libraries on-line. These {custom} libraries give the builders extra flexibility and management over the interior workings of their implant, in comparison with open-source options. Additionally they manifest sure unpredictable behaviors that pressured us to dig deep into the code to know. Examples of those {custom} libraries are HTTPAccess and ManagedCookie.
HTTPAccess offers mandatory features to deal with all of the HTTP communications of CloudScout modules. It has the potential of modifying HTTP headers, as proven in Determine 9.
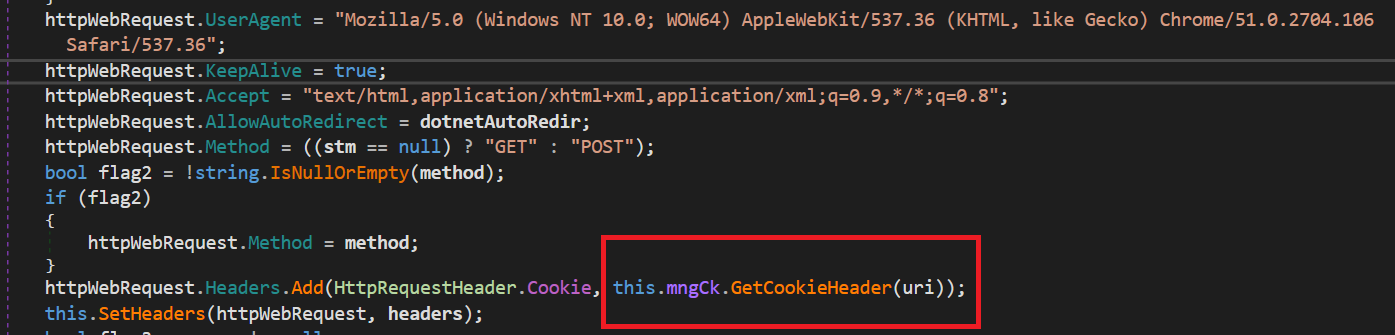
As highlighted on this code snippet, the this.mngCk object, an occasion of the ManagedCookie class, is used to combine cookies into the crafted HTTP headers. Because the title suggests, ManagedCookie offers features to handle cookies for net requests between CloudScout and focused cloud companies. What makes this class particular is its complete listing of cookie parsers able to turning most cookies into default .NET cookie objects. Determine 10 exhibits the completely different regexes created to match numerous mixtures of attribute-value pairs in cookies.
The body of CloudScout
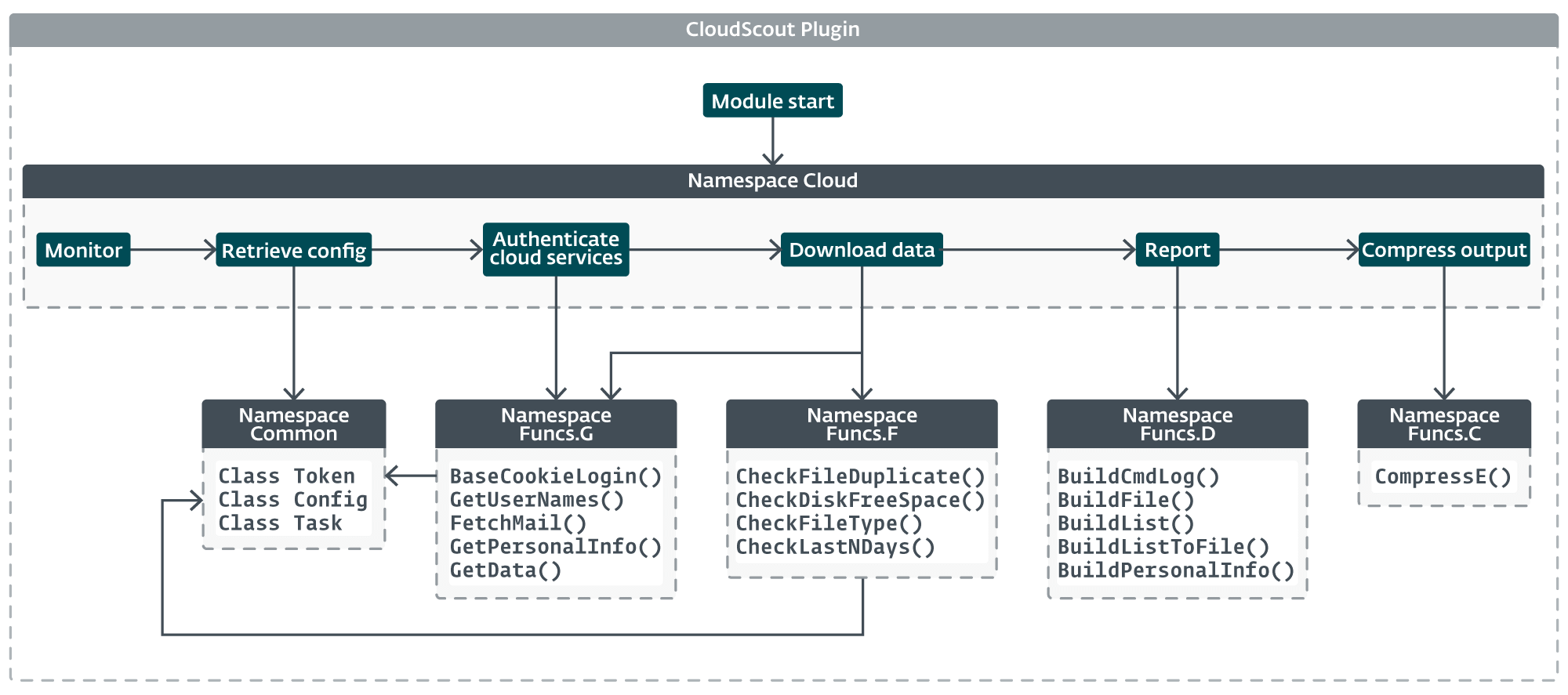
All CloudScout modules share a uniform structure, as proven in Determine 11. The core performance of the module is within the Cloud namespace, which is almost similar in every module. The implementation solely diverges in features associated to authentication and information retrieval, the place every module must generate particular net requests or to parse sure net responses in response to the cloud service it targets.
The streamlined design of CloudScout and the core logic of the Cloud namespace is illustrated in Determine 12.
Authentication
Cookies on the whole are usually not very properly documented by net platforms. Authentication cookies are inclined to have brief lifespans and are regularly up to date because the consumer interacts with the platform through an internet browser. Nevertheless, so long as the periods are nonetheless legitimate, the cookies listed in Desk 4 will be abused by CloudScout to entry and obtain useful information from cloud companies.
Desk 4. Authentication cookies dealt with by the CloudScout modules
| Service | Area | Required cookies |
| Google Drive | drive.google.com accounts.google.com |
OSID, HSID, SID, SSID, APISID, SAPISID, LSID |
| Gmail | mail.google.com accounts.google.com |
|
| Outlook | outlook.stay.com login.stay.com |
X-OWA-CANARY, RPSSecAuth, ClientId |
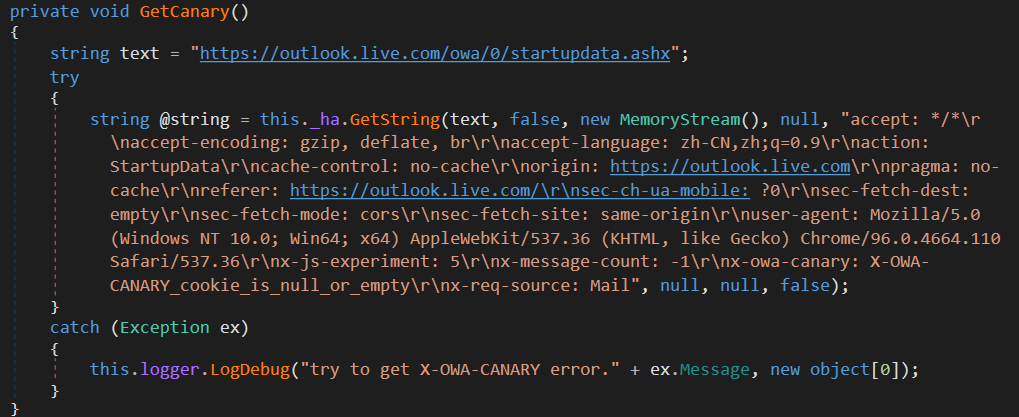
X-OWA-CANARY is a safety cookie utilized by Microsoft Outlook Internet Entry (OWA) to stop cross-site request forgery assaults. It’s assigned firstly of every session when the consumer is authenticated. CloudScout’s COL module implements a mechanism to retrieve this cookie when it isn’t out there, by establishing a brand new session utilizing the RPSSecAuth and ClientId cookies to reauthenticate, as proven in Determine 13.
Information retrieval
After authentication, the CloudScout modules browse the compromised cloud service accounts in a way much like how an everyday consumer would with an internet browser. To attain this, every CloudScout module is provided with a set of hardcoded net requests to carry out, together with advanced HTML parsers, which determine and extract the information of curiosity from the online responses.
For instance, the CGM and COL modules are focused on mail folder listings and electronic mail messages, concentrating on Gmail and Outlook, respectively. Determine 14 exhibits the steps that CGM performs to extract electronic mail headers, electronic mail our bodies, and attachments from the HTML content material served by the Gmail net server.
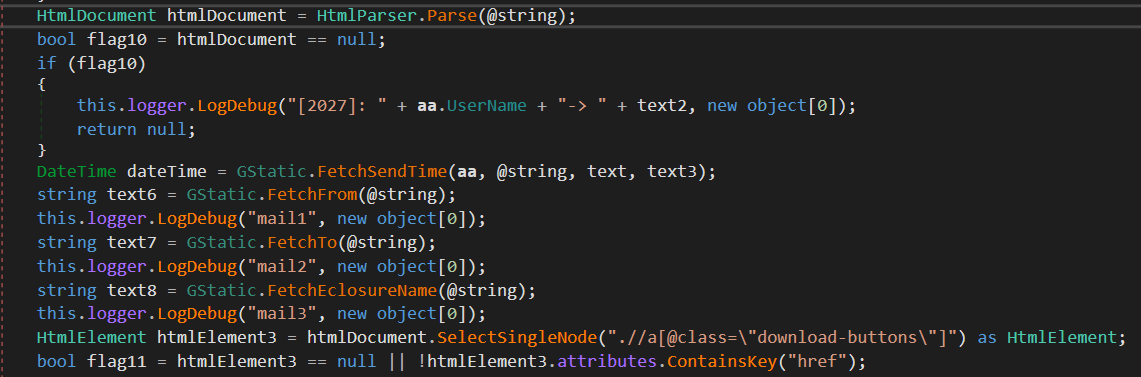
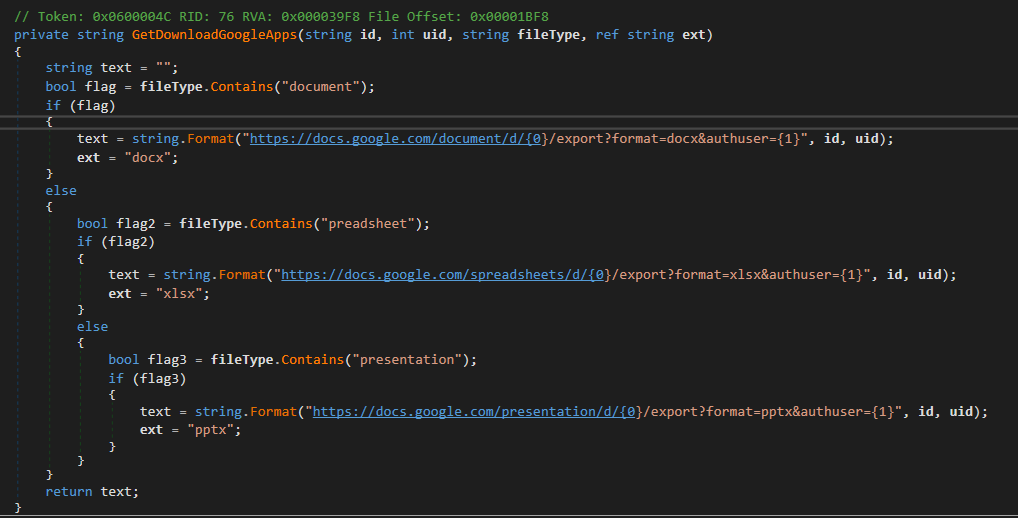
Then again, CGD is focused on consumer info from Google Drive; a full listing hierarchy; and recordsdata with extensions .doc, .docx, .xls, .xlsx, .ppt, .pptx, .pdf, and .txt. Determine 15 is the code snippet from CGD to generate a obtain URL for a doc.
The module appends a {custom} header to every downloaded merchandise, whether or not it’s a file or an electronic mail. This practice header contains metadata of the merchandise corresponding to consumer ID (assigned by the malware), electronic mail topic, or filename, and the username of the cloud service (Desk 5). The added header almost certainly permits stolen information to be processed at scale, by automated programs, for fast indexing or to carry out evaluation.
Desk 5. Customized headers for downloaded electronic mail and recordsdata
| Mail header | File header |
| tasktype: taskid: clientid: objectname: mailid: username: topic:=?utf-8?b? froms:=?utf-8?b? tos:=?utf-8?b? kind: sourceflag: Gmail filepath: mailcountry: attachment: mailboxtype:gmail folder:=?utf-8?b? time: captime: |
tasktype: taskid: clientid: objectname: username: skydrivetype:googledrive path:=?utf-8?b? ? supply:googledrive filename:=?utf-8?b? ? key: filetime: dimension: kind:googledrive captime: |
After including the header, every merchandise is encrypted utilizing the identical RC4 key as used for the configuration file and saved with the filename
Desk 6. Filename extension for every information class
| Information class | CGD | CGM or COL |
| Private info | .pc_plug_googledrive_profile | N/A |
| Electronic mail | N/A | .pc_plug_gmck_email |
| Listing itemizing | .pc_plug_googledrive_filelist | .pc_plug_gmck_email_list |
| File | .pc_plug_googledrive_file | N/A |
Subsequent, all objects are compressed right into a ZIP archive named
Conclusion
CloudScout is a .NET toolset utilized by Evasive Panda to steal information saved in cloud companies. It’s applied as an extension to MgBot and makes use of the pass-the-cookie approach to hijack authenticated periods from net browsers.
On this blogpost, now we have highlighted the skilled design behind the CloudScout framework to exhibit Evasive Panda’s technical capabilities and the necessary roles that cloud-stored paperwork, consumer profiles, and electronic mail play in its espionage operations.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis presents non-public APT intelligence studies and information feeds. For any inquiries about this service, go to the ESET Menace Intelligence web page.
IoCs
A complete listing of indicators of compromise (IoCs) and samples will be present in our GitHub repository.
Information
| SHA-1 | Filename | Detection | Description |
| C70C3750AC6B9D7B033A |
pmsrvd.dll | Win32/Agent.AELQ | MgBot loader. |
| 812124B84C5EA455F714 |
pmsrvd.dll | Win32/Agent.AELQ | MgBot loader. |
| AD6C84859D413D627AC5 |
3.exe | Win32/Agent.ADJV | MgBot dropper. |
| 3DD958CA6EB7E8F0A061 |
1.exe | Win32/Agent.ADJV | MgBot dropper. |
| 547BD65EEE05D744E075 |
doc.exe | Win32/Agent.AFXX | Nightdoor dropper. |
| 348730018E0A5554F0F0 |
DJCU.dll | Win32/Nightdoor.A | Nightdoor loader. |
| 9B6A473820A72111C1A3 |
CommonUtilities.dll | MSIL/Agent.UEK | CloudScout inner library package deal model 1.0.0. |
| 621E2B50A979D77BA3F2 |
CGM.dll | MSIL/CloudScout.A | CloudScout Gmail stealer model 1.0.14. |
| C058F9FE91293040C8B0 |
CGM.dll | MSIL/CloudScout.A | CloudScout Gmail stealer model 1.0.13. |
| 4A5BCDAAC0BC315EDD00 |
CGM.dll | MSIL/CloudScout.A | CloudScout Gmail stealer model 1.0.18. |
| 67028AEB095189FDF18B |
CGD.dll | MSIL/CloudScout.A | CloudScout Google Drive stealer model 1.0.11. |
| B3556D1052BF5432D39A |
CGD.dll | MSIL/CloudScout.A | CloudScout Google Drive stealer model 1.0.14. |
| 84F6B9F13CDCD8D9D15D |
CGD.dll | MSIL/CloudScout.A | CloudScout Google Drive stealer model 1.0.17. |
| 93C1C8AD2AF64D0E4C13 |
COL.dll | MSIL/CloudScout.A | CloudScout Outlook Internet Entry stealer model 1.0.10. |
| 8EAA213AE4D482938C5A |
CommonUtilities.dll | MSIL/CloudScout.A | CloudScout inner library package deal model 1.0.8. |
| A1CA41FDB61F03659168 |
CommonUtilities.dll | MSIL/CloudScout.A | CloudScout inner library package deal model 1.0.11. |
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
| 103.96.128[.]44 | N/A | IRT-WUZHOUHULIAN-HK | 2022-05-26 | MgBot and Nightdoor C&C server. |
MITRE ATT&CK methods
This desk was constructed utilizing model 15 of the MITRE ATT&CK framework.
| Tactic | ID | Title | Description |
| Useful resource Improvement | T1583.004 | Purchase Infrastructure: Server | Evasive Panda acquired servers for the C&C infrastructure of MgBot and Nightdoor. |
| T1587.001 | Develop Capabilities: Malware | Evasive Panda developed {custom} implants corresponding to MgBot, CloudScout, and Nightdoor. | |
| Execution | T1569.002 | System Companies: Service Execution | MgBot is executed as a Home windows service. |
| T1106 | Execution via API | The MgBot installer makes use of Home windows APIs to create processes. Gmck makes use of ExecuteInDefaultAppDomain to execute CGM within the CLR. | |
| Persistence | T1543.003 | Create or Modify System Course of: Home windows Service | MgBot replaces the present Software Administration service DLL path with its personal. |
| Privilege Escalation | T1548.002 | Abuse Elevation Management Mechanism: Bypass Consumer Entry Management | MgBot performs UAC bypass. |
| Protection Evasion | T1140 | Deobfuscate/Decode Information or Data | Gmck decrypts Chrome, Edge, and Firefox net browser databases to extract cookies. |
| T1112 | Modify Registry | MgBot modifies the registry for persistence. | |
| T1027 | Obfuscated Information or Data | Gmck obfuscates the configuration that accommodates cookies. | |
| T1550.004 | Use Alternate Authentication Materials: Internet Session Cookie | CloudScout makes use of stolen cookies to entry cloud sources. | |
| T1036.005 | Masquerading: Match Reliable Title or Location | CloudScout modules are put in to %ProgramDatapercentNVIDlA to imitate an NVIDIA listing. | |
| Credential Entry | T1539 | Steal Internet Session Cookie | Gmck steals cookies. |
| Discovery | T1082 | System Data Discovery | MgBot collects system info. |
| Assortment | T1560.001 | Archive Collected Information: Archive through Utility | CloudScout modules use SharpZipLib to compress information earlier than exfiltration. |
| T1530 | Information from Cloud Storage Object | CGD downloads recordsdata saved on Google Drive. | |
| T1114.002 | Electronic mail Assortment: Distant Electronic mail Assortment | CGM and COL entry and acquire emails from Gmail and Outlook Internet Entry, respectively. | |
| Command and Management | T1095 | Non-Software Layer Protocol | MgBot communicates with its C&C through UDP. |
| Exfiltration | T1041 | Exfiltration Over C2 Channel | MgBot exfiltrates collected information to its C&C. |
[ad_2]



