Hackers have been noticed utilizing search engine optimization poisoning and search engine ads to advertise faux Microsoft Groups installers that infect Home windows units with the Oyster backdoor, offering preliminary entry to company networks.
The Oyster malware, often known as Broomstick and CleanUpLoader, is a backdoor that first appeared in mid-2023 and has since been linked to a number of campaigns. The malware gives attackers with distant entry to contaminated units, permitting them to execute instructions, deploy further payloads, and switch recordsdata.
Oyster is often unfold by way of malvertising campaigns that impersonate common IT instruments, comparable to Putty and WinSCP. Ransomware operations, like Rhysida, have additionally utilized the malware to breach company networks.
Faux Microsoft Groups installer pushes malware
In a brand new malvertising and search engine optimization poisoning marketing campaign noticed by Blackpoint SOC, menace actors are selling a faux web site that seems when guests seek for “Groups obtain.”
Supply: Blackpoint
Whereas the adverts and area don’t spoof Microsoft’s area, they result in an internet site at teams-install[.]high that impersonates Microsoft’s Groups obtain web site. Clicking on the obtain hyperlink would obtain a file referred to as “MSTeamsSetup.exe,” which is identical filename utilized by the official Microsoft obtain.
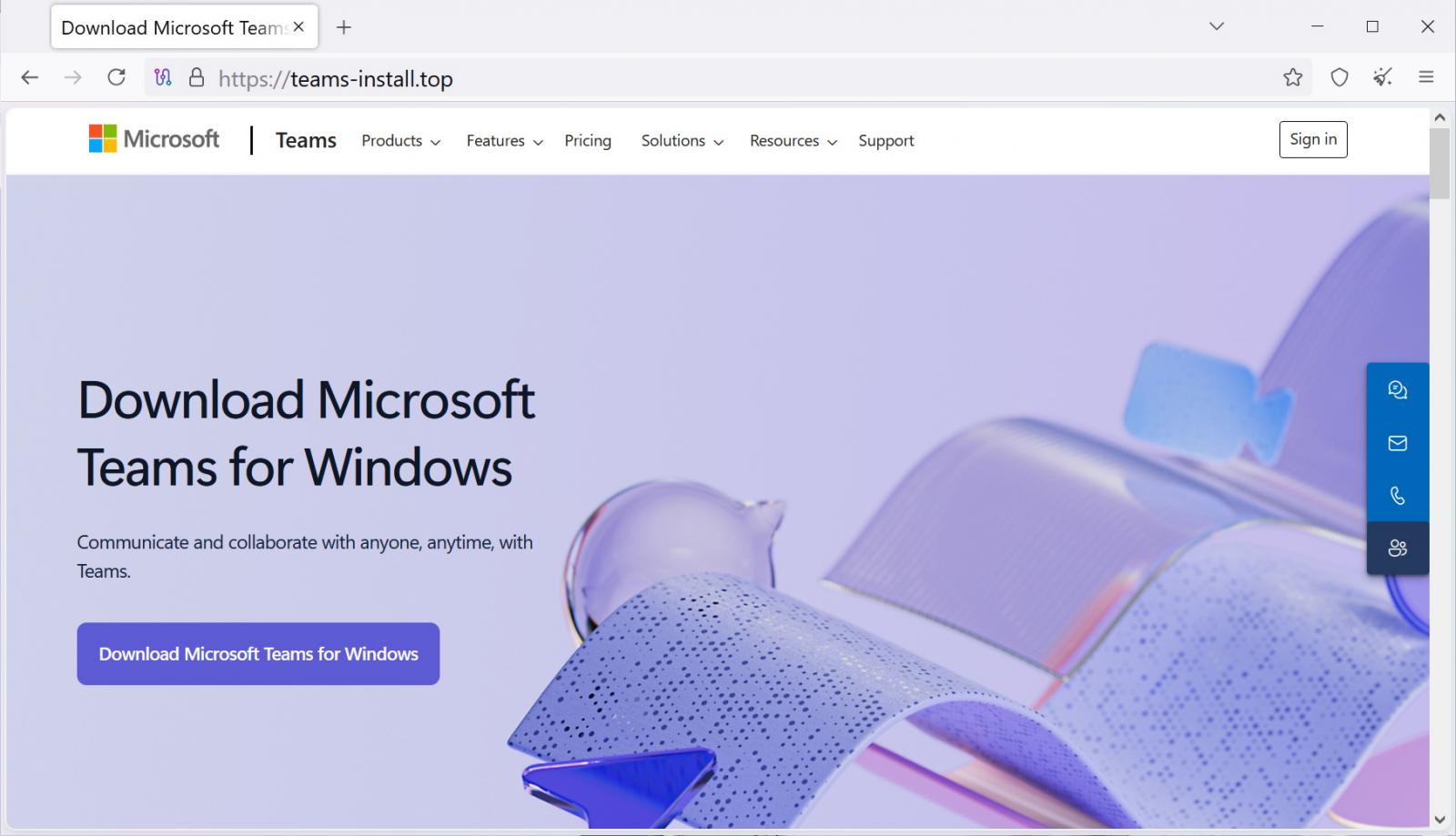
Supply: Blackpoint
The malicious MSTeamsSetup.exe [VirusTotal] was code-signed with certificates from “4th State Oy” and “NRM NETWORK RISK MANAGEMENT INC” so as to add legitimacy to the file.
Nevertheless, when executed, the faux installer dropped a malicious DLL named CaptureService.dll [VirusTotal] into the %APPDATApercentRoaming folder.
For persistence, the installer creates a scheduled job named “CaptureService” to execute the DLL each 11 minutes, making certain the backdoor stays lively even on reboots.
This exercise resembles earlier faux Google Chrome and Microsoft Groups installers that pushed Oyster, highlighting how search engine optimization poisoning and malvertising stay a preferred tactic for breaching company networks.
“This exercise highlights the continued abuse of search engine optimization poisoning and malicious ads to ship commodity backdoors beneath the guise of trusted software program,” concludes Blackpoint.
“Very similar to the faux PuTTY campaigns noticed earlier this 12 months, menace actors are exploiting person belief in search outcomes and well-known manufacturers to achieve preliminary entry.”
As IT admins are a preferred goal for getting access to credentials with excessive privileges, they’re suggested solely to obtain software program from verified domains and to keep away from clicking on search engine ads.


